In this blog, we explain the purpose of Clause 6.3 from ISO 27001 and why planned, well governed information security management system (ISMS) change management is essential for maintaining effective information security. We outline the types of ISMS changes the Clause applies to and describe the risks that arise when changes are not controlled. The blog also explores key considerations for putting Clause 6.3 into practice, from defining change management processes to assessing risks, testing changes and establishing strong governance.
For an ISMS to be effective, it must be capable of responding to the organisation’s security risks. Since the security threat landscape is ever evolving, it will often be necessary for an ISMS to be adapted so that the organisation can remain resilient to compromise. However, such changes should only ever be carried out in a controlled and deliberate manner; otherwise, they risk introducing new security threats. Clause 6.3 of ISO 27001 addresses this issue, requiring organisations to take pre-defined steps to ensure changes to the ISMS are carried out responsibly.
What does Clause 6.3 require?
Clause 6.3 is not one of the longer, more detailed ISO 27001 clauses and simply states that ‘When the organization determines the need for changes to the information security management system, the changes shall be carried out in a planned manner’. Examples of such changes include:
- Making policy revisions
- Introducing new technology
- Installing software patches
- Relocating to new premises
- Changing roles and responsibilities
- Revising software code.
Organisations must define the steps that need to be taken so that any changes proposed are properly submitted, reviewed, approved, and implemented, and such steps need to be decided before any ISMS changes can take place. This reduces the impact and likelihood of new security threats being accidentally introduced, as well as ensuring that relevant stakeholders are notified and consulted on changes as necessary. An organisation that fails to define these steps puts itself at risk of poor user awareness, reduced data oversight, and shadow IT (including vulnerable or malicious software deployments); these are just some examples of what can happen if changes to the ISMS are not properly controlled.
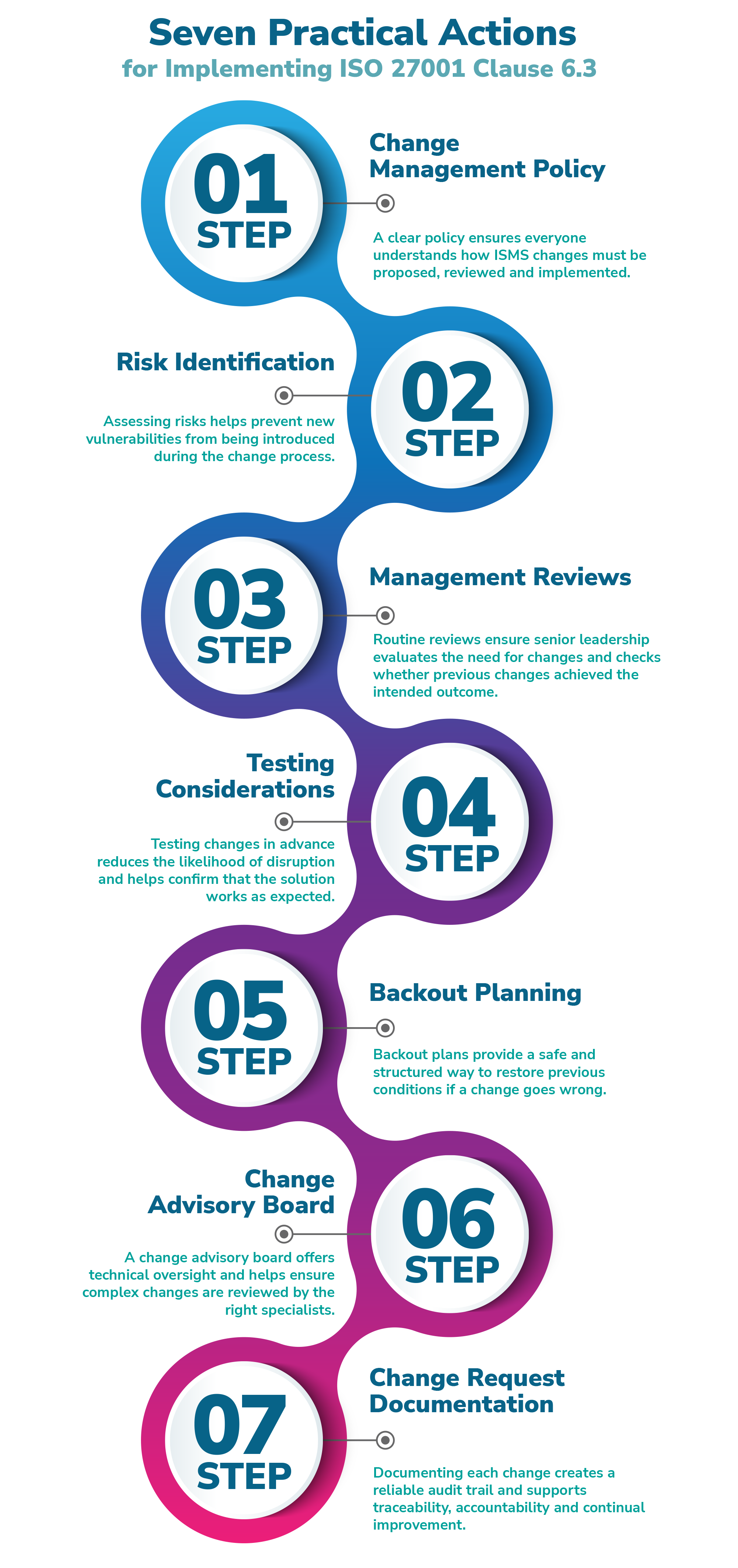
Seven Practical Actions for Implementing Clause 6.3
Whilst Clause 6.3 does not state specifically how organisations should manage changes to the ISMS in practice, we recommend taking the following actions.
1. Create a change management policy
Having a change management policy or an equivalent document ensures that your change management requirements are both documented and easy to communicate to the wider team. Such a document should cover details such as:
- How change proposals are submitted – who can submit them, how they should be submitted, and who they go to
- Key roles and responsibilities – who reviews proposals, who approves or rejects them, and who is responsible for implementation and reporting
- Where changes must be logged – for example, in a change log or ticketing system
Depending on the nature of your organisation, you may need different change management processes for different types of changes. For example, a software company may require a separate procedure for managing new software development, and changes involving third party suppliers may follow their own process. Whatever the approach, it’s important that the steps you take to control ISMS changes are documented and communicated to the relevant stakeholders.
2. Identify any information security risks associated with proposed changes
A lack of visibility over changes to your ISMS can significantly affect its ability to safeguard your information assets. To maintain visibility, you should formally assess whether a proposed change could put information assets at risk of unauthorised access, disclosure, modification, deletion or removal. You should also consider the likelihood and impact of any risks identified.
3. Conduct regular management reviews (see Clause 9.3)
Clause 9.3 requires senior management to regularly review the performance of the ISMS, using a standard agenda that includes opportunities for improvement and any changes needed to the ISMS. This includes changes in the needs and expectations of interested parties, as well as a standing agenda item for continual improvement. The Clause also requires documented information explaining what was discussed, which provides an opportunity to record changes considered, decisions made and any follow up actions. By reviewing actions from previous meetings, Clause 9.3 also ensures that the success of approved changes is evaluated at the next review.
4. Consider the need for change testing
Testing certain changes before implementation helps identify whether the proposal works in practice and highlights any issues early. It also helps uncover additional areas for improvement and increases the likelihood of a successful change. For example, an organisation considering an endpoint detection and response (EDR) tool could trial different products using demos or free trials to assess whether they meet organisational needs and offer additional benefits.
5. Consider the need for backout plans
Even well planned changes can have unintended consequences. When planning a change to the ISMS, it’s important to consider how the organisation will respond if something goes wrong after implementation. For example, if you plan to roll out multi factor authentication (MFA) across all systems, how will you revert the change if MFA causes system failures or performance issues? Having clear backout plans ensures you can restore the ISMS to its previous state while investigating the issue or identifying an alternative solution.
6. Consider the need for a change advisory board
For technical changes (such as software patches or code updates), it can be helpful to appoint a change advisory board (CAB), i.e., a group of technical specialists who can assess, test and approve changes. A CAB may meet regularly or be convened on an ad hoc basis. Technical changes are also covered under Control A.8.32 of ISO 27001, which addresses changes to information processing facilities and information systems.
7. Have a change request form or ticketing system
Documenting proposed changes is an important part of planning, as it ensures key information is recorded throughout the process. Useful details include:
- A unique reference
- Date raised
- Description of the change
- Change owner (and implementer, if different)
- Approver(s)
- Risk assessments and backout arrangements
- Testing arrangements
- Links to incident management, if relevant
- Completion and closure dates
- Post change analysis or evaluation
Keeping a clear record of changes allows you to track progress over time and maintain an accurate change log.
Conclusion
Control over ISMS change management, far from being constrictive or cumbersome, is an effective business enabler. It provides clarity about how changes shall be submitted, reviewed, approved and implemented over time. It also ensures that key roles and responsibilities are defined and that all changes are handled by competent personnel. Further, since Clause 6.3 of ISO 27001 allows organisations to determine their own change management steps, it enables you to manage ISMS changes in as flexible or as structured a manner as you need.
By ensuring changes to the organisation’s ISMS are carried out responsibly, your organisation can strengthen the security of its information assets, become more resilient to threats, and enhance the efficacy of its ISMS.
How URM Can Help
With 20 years of experience assisting organisations’ ISO 27001 implementation, URM is the ideal partner to support any aspect of your organisation’s conformance/certification to the Standard. Our expert team can offer a range of ISO 27001 support services to help you fully conform to the Standard’s requirements. We can conduct an ISO 27001 gap analysis where we establish your current level of conformance, and help you conduct your risk assessment using our proven risk assessment tool, Abriska 27001. Following this, we can work with you to develop policies, processes and ISMS infrastructure that meet both the Standard’s requirements and your organisation’s unique needs. URM can also offer ISO 27001 internal audit services, including conducting an internal audit ahead of your certification assessment to ensure your organisation is conformant, planning and implementing a full 3-year ISO 27001 audit programme, or auditing more specific aspects of the ISMS or particular controls.
In addition to our consultancy services, URM regularly delivers ISO 27001-related training courses. Our Introduction to ISO 27001 Course explores all aspects of information security and the importance of ISO 27001 in protecting information, whilst our Certificate in Information Security Management Principles (CISMP) Training Course will fully prepare you to sit and pass the BCS-invigilated examination and gain an industry-recognised information security qualification.
A short, free, non‑commitment call can help you clarify scope, understand regulatory expectations, and align your approach across standards such as ISO 42001 and NIST AI RMF. Early guidance often saves time and avoids fragmented compliance efforts.
Whether you are at an early planning stage or preparing for audit and assurance activities, we offer a free introductory call to help you assess risks, responsibilities, and the most proportionate route forward.
You do not need a fully defined programme to start the conversation. We offer a free, no‑obligation call to help you understand SOC 2 requirements, assess your current position, and identify practical next steps.

Executing your decision to use an information security management system (ISMS) to manage the security of your information assets is a project. It is not.

In this blog, we’re going back to basics and looking at some of the fundamentals of information security and ISO 27001.

A question which comes up time and time again is ‘How do I approach asset identification within my information security risk assessment’.